The 2026 Unit 42 Global Incident Response Report delivers a sharp wake-up call: Threat actors are now moving 4x faster to exfiltration than in 2025. By striking across three or more surfaces simultaneously, adversaries are intentionally exploiting the blind spots created by an over-reliance on endpoint data.
While the endpoint remains a critical first line of defense, the rapid proliferation of cloud services, microservices and remote users has expanded the attack surface beyond what any single tool can monitor. In 75% of incidents Unit 42 investigated, critical evidence of the initial intrusion was present in the logs. Yet, due to complex, disjointed systems, that information wasn't readily accessible or effectively operationalized, allowing attackers to exploit the gaps undetected. To stay ahead, SOCs must evolve to ingest and correlate telemetry across the entire organizational landscape.
The Invisible Pivot
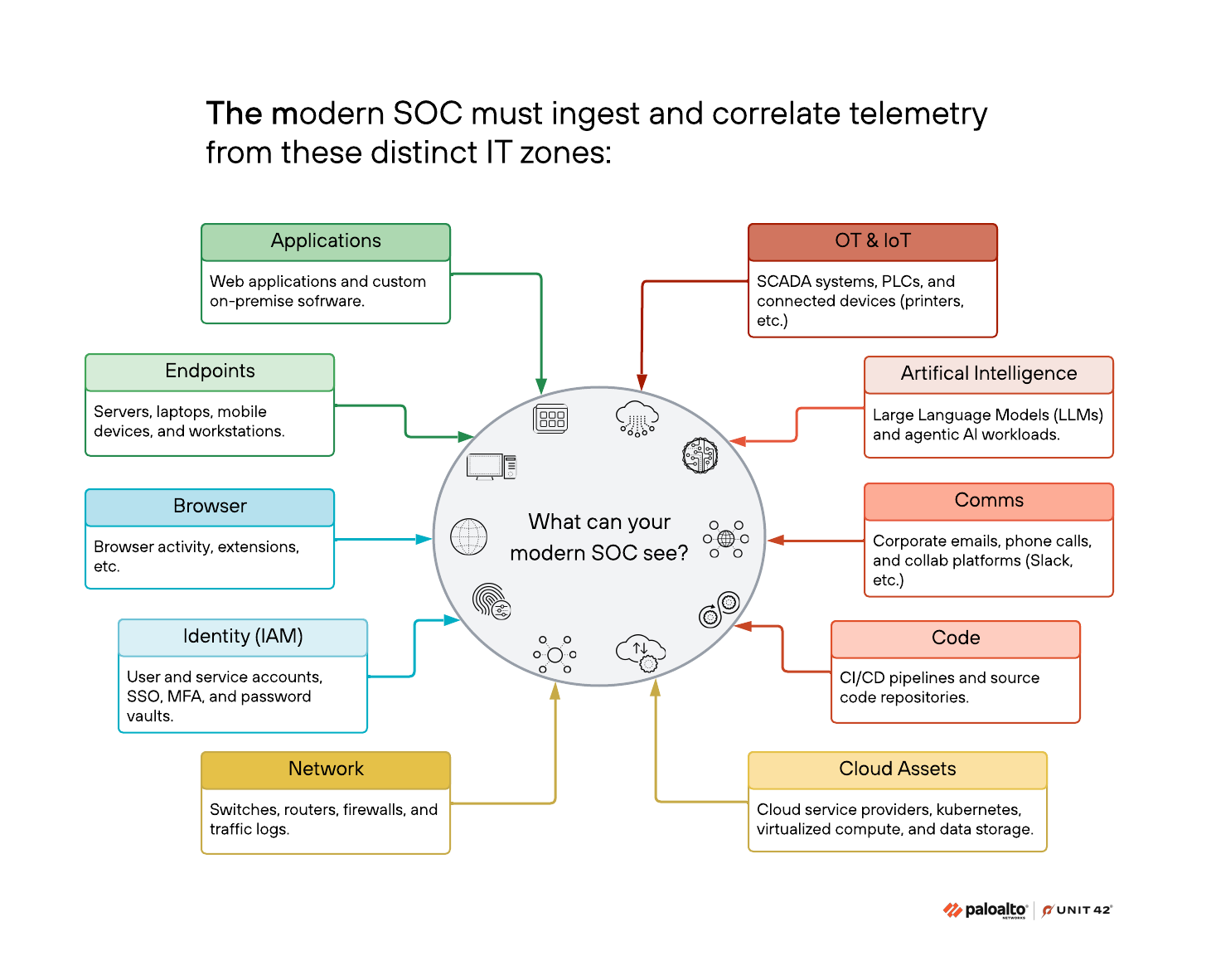
Generally, IT environments are composed of distinct zones. These include identity and access management (IAM), cloud assets and operational technology (OT), internet of things (IoT) and AI workloads, each with its own built-in logging and security needs. Specific security tools are produced to protect the assets in each of these zones. Therefore, SOCs should be able to holistically analyze the logs and alerts from each of these zones and utilize the corresponding security tools to take action against threats. While an endpoint detection and response (EDR) centric approach is a foundational element of, relying on any EDR alone creates gaps that attackers use to move invisibly. These zones are visualized in Figure 1.
Unit 42 research has identified three specific scenarios where an endpoint-only view consistently fails to tell the full story:
1. The cloud-to-endpoint pivot: In scenarios when attackers gain access via a misconfigured cloud service access key, they may be able to pivot to endpoints while hiding their tracks from EDR agents. From the cloud console, they could pivot to a cloud-hosted server to begin discovery. To a SOC only watching the endpoint, the initial entry and console manipulation are invisible, and the attacker’s activity may appear as a legitimate login, increasing the chance of the SOC reporting a false negative when triaging this event. Detection requires stitching together cloud security logs, CASB alerts and EDR telemetry to reveal the full narrative of the breach.
2. Covert C2 and identity theft: Imagine an attacker using DNS tunneling to a cloud storage location to control a compromised device. To use legitimate applications to mask their activity, they must steal credentials and may trigger impossible travel alerts across multiple software-as-a-service (SaaS) apps. If the SOC is only looking for malware on the device, they will miss the identity-level compromise happening across the network and cloud providers.
3. The threat of rogue assets: Shadow IT and unmanaged devices are inherently opaque. Because these devices often lack security agents, they are frequently invisible to traditional EDR and security information and event management tools. Attackers often introduce their own rogue devices to maintain persistence. Without continuous network monitoring and external attack surface management, these assets remain open doors for covert movement.
Building a Single Pane of Glass: Unit 42’s View of a Modern SOC
Figure 2 illustrates Palo Alto Networks' vision for a SOC built on a unified, AI-driven data platform.
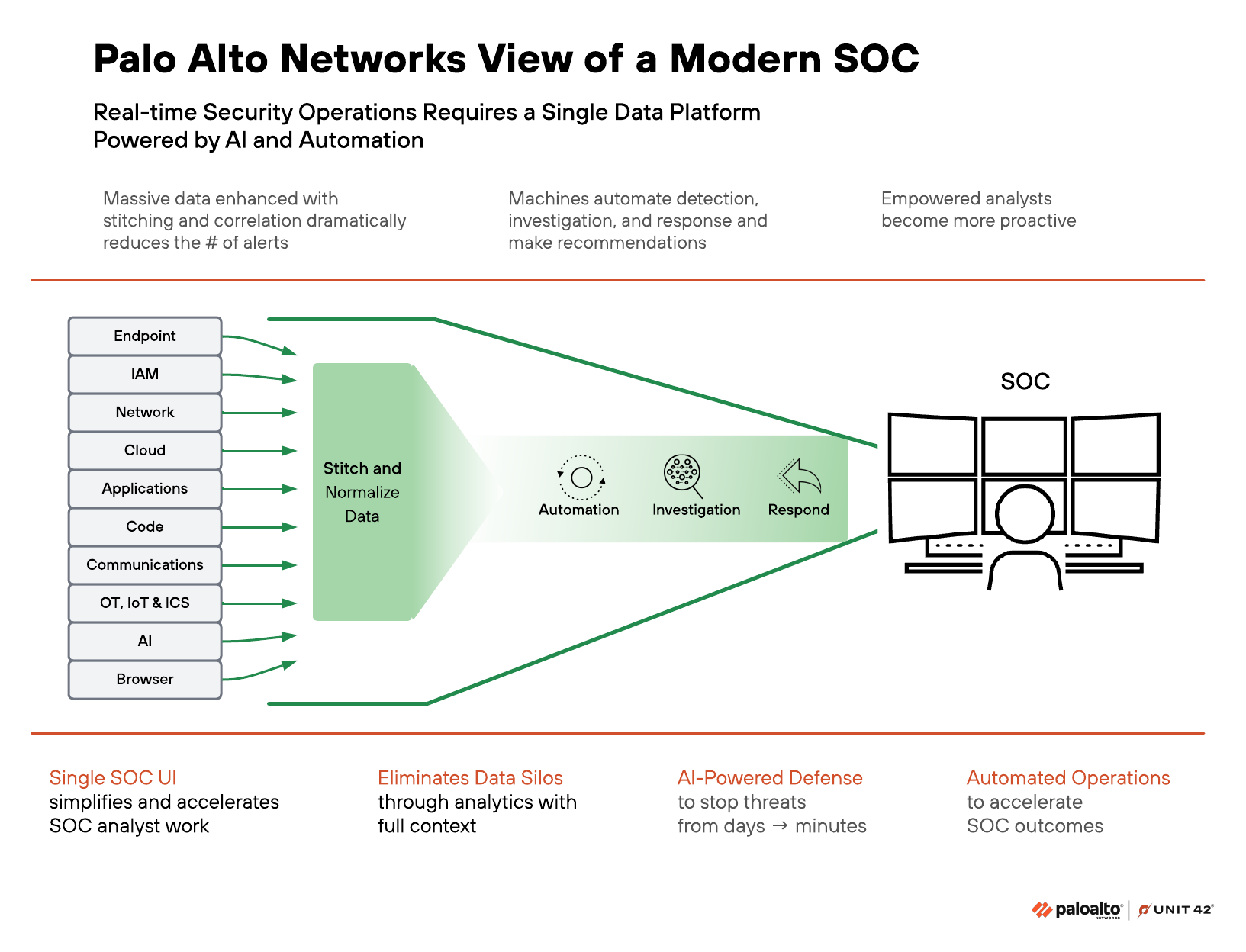
By consolidating diverse security data and using AI to automate detection, investigation and response, the platform significantly reduces alert fatigue and eliminates data silos. Ultimately, this shifts the heavy lifting to machines, empowering human analysts with a single, simplified interface to proactively stop threats in minutes rather than days.
To combat these threats, Unit 42 recommends a single-pane-of-glass strategy powered by an AI-driven SOC platform like Cortex XSIAM. This approach is built on two core principles: All security logs must live in a single repository, and all alerts must be processed in a centralized workbench.
By integrating data from all 10 IT zones — including code, comms and AI — the SOC can leverage machine learning for:
- Alert stitching: Automatically connecting events from different zones into a cohesive timeline
- ML-based incident scoring: Prioritizing threats based on business impact and user risk
- User and entity behavior analytics: Detecting anomalous behavior that signals compromised credentials before they result in a material impact
This integration improves the lives of analysts by reducing alert fatigue and providing management with clear visibility into workloads and performance metrics.
Final Thoughts
As we expect attackers to continue to use AI-assisted tools to increase the speed of attacks; relying solely on the endpoint is no longer a viable strategy for the modern enterprise. By embracing a unified platform that ingests and correlates telemetry from every IT zone, organizations can gain the holistic visibility needed to stop sophisticated threats in their tracks.
The transition to an AI-enabled, multi-surface defense is the only way to turn the tide against attackers who thrive in the gaps between isolated tools. To ensure your SOC is optimally equipped for this challenge, consider evaluating your current visibility through a formal assessment.
Unit 42 Frontier AI Defense is an elite service that uses access to frontier models to identify your organization's likely attack paths before attackers can weaponize them.
Additional Resources
- Know Ourselves Before Knowing Our Enemies: Threat Intelligence at the Expense of Asset Management – Unit 42, Palo Alto Networks
- When a Zero Day and Access Keys Collide in the Cloud: Responding to the SugarCRM Zero-Day Vulnerability – Unit 42, Palo Alto Networks
- Cloud Logging for Security and Beyond – Unit 42, Palo Alto Networks
- 2025 Unit 42 Global Incident Response Report – Unit 42, Palo Alto Networks









 Get updates from Unit 42
Get updates from Unit 42