Executive Summary
Update: March 26, 2026
As the conflict continues to evolve in the Middle East, Unit 42 is providing an update to the cyberthreat activity we are tracking since the publication of this threat brief. As of March 26, 2026, Iran has surpassed its 27th straight day of near complete internet blackout.
Recent Destructive Attacks
Unit 42 is tracking an increased risk of wiper attacks related to the conflict with Iran. Iranian actors have a history dating back to 2012 of conducting destructive attacks against high priority targets, highlighting a pattern of capability and intent.
Unit 42 conducted an in-depth investigation into conflict-themed phishing lures identifying 7,381 related phishing URLs spanning 1,881 unique hostnames.
Recent threat activity demonstrates a widespread wave of financial fraud, credential harvesting and illicit content distribution targeting both enterprise and consumer sectors. Threat actors are heavily relying on the impersonation of highly trusted entities including major telecommunications providers, national airlines, law enforcement and critical energy corporations, to deceive victims.
The operations leverage agile evasion tactics, including top-level domain rotation, subdomain chaining and purpose-built infrastructure designed to mimic official corporate portals and government payment workflows. Furthermore, attackers are opportunistically exploiting current geopolitical events with conflict-themed lures to facilitate widespread donation and cryptocurrency scams. Ultimately, this activity highlights a sophisticated, multi-pronged approach to exploiting regional brand trust for financial and data theft.
We discuss these details in more detail in the section Current Scope of the Attacks – March 2026.
March 2, 2026
On Feb. 28, 2026, the United States and Israel launched a significant joint offensive code named Operation Epic Fury (U.S.) and Operation Roaring Lion (Israel). In the hours following the initial strikes, Iran began a multi-vector retaliatory campaign, which has evolved into a significant transregional conflict. Unit 42 has observed an escalation in cyberattacks from activists outside the country. However, we believe threat activity from nation-state groups based within the country is mitigated in the near term because of the limited internet connectivity in Iran.
Beginning the morning of Feb. 28, 2026, Iran’s available internet connectivity dropped to between 1%-4%. We assess that the loss of connectivity and significant degradation of Iranian leadership and command structures will likely hinder the ability of state-aligned threat actors to coordinate and execute sophisticated cyberattacks in the near-term.
State-aligned cyber units may be acting in operational isolation, which could result in deviations from previously established patterns. Additionally, Iranian command and control degradation may also lead to tactical autonomy for cells outside of Iran. However, the capacity to sustain sophisticated cyber operations is likely reduced due to the operational disruptions.
For Iran-aligned threat actors based outside of the region, we assess that hacktivist groups will target organizations perceived as adversaries but their impact is likely to be of low to medium significance. Other nation-state-aligned threat actors may attempt to exploit the situation to activate cyberattacks to further their own interests.
Geographically dispersed operators and affiliated cyber proxies may also target governments in regions hosting U.S. military bases to disrupt logistics. In the near term, these activities are expected to consist of low-to-medium sophistication disruptions (for example, distributed denial of service and hack and leak campaigns).
For details on Unit 42’s previous observations of cyber activity linked to Iran-backed groups and hacktivists see the Threat Brief: Escalation of Cyber Risk Related to Iran (Updated June 30). That report details Iran-backed groups and hacktivists expanding their global cyber operations using website defacement, distributed-denial-of-service (DDoS) attacks, and data exfiltration and wiper attacks. The primary objectives of Iran-aligned nation-state actors frequently include espionage and disruption. Techniques include using AI-enhanced targeted spear-phishing campaigns, the exploitation of known vulnerabilities, and the use of covert infrastructure for espionage.
Palo Alto Networks customers can receive protections from and mitigations for relevant threat actor activity through the following products and services:
- Next-Generation Firewalls with Advanced Threat Prevention
- Advanced URL Filtering and Advanced DNS Security identify known URLs and domains associated with this activity as malicious
- Cortex XDR, XSIAM and Cortex Cloud
The Unit 42 Incident Response team can also be engaged to help with a compromise or to provide a proactive assessment to lower your risk.
| Related Unit 42 Topics | Hacktivism, DDoS Attacks, Wipers, Phishing |
Current Scope of Cyberattacks – March 2026
Conflict-Themed Domains
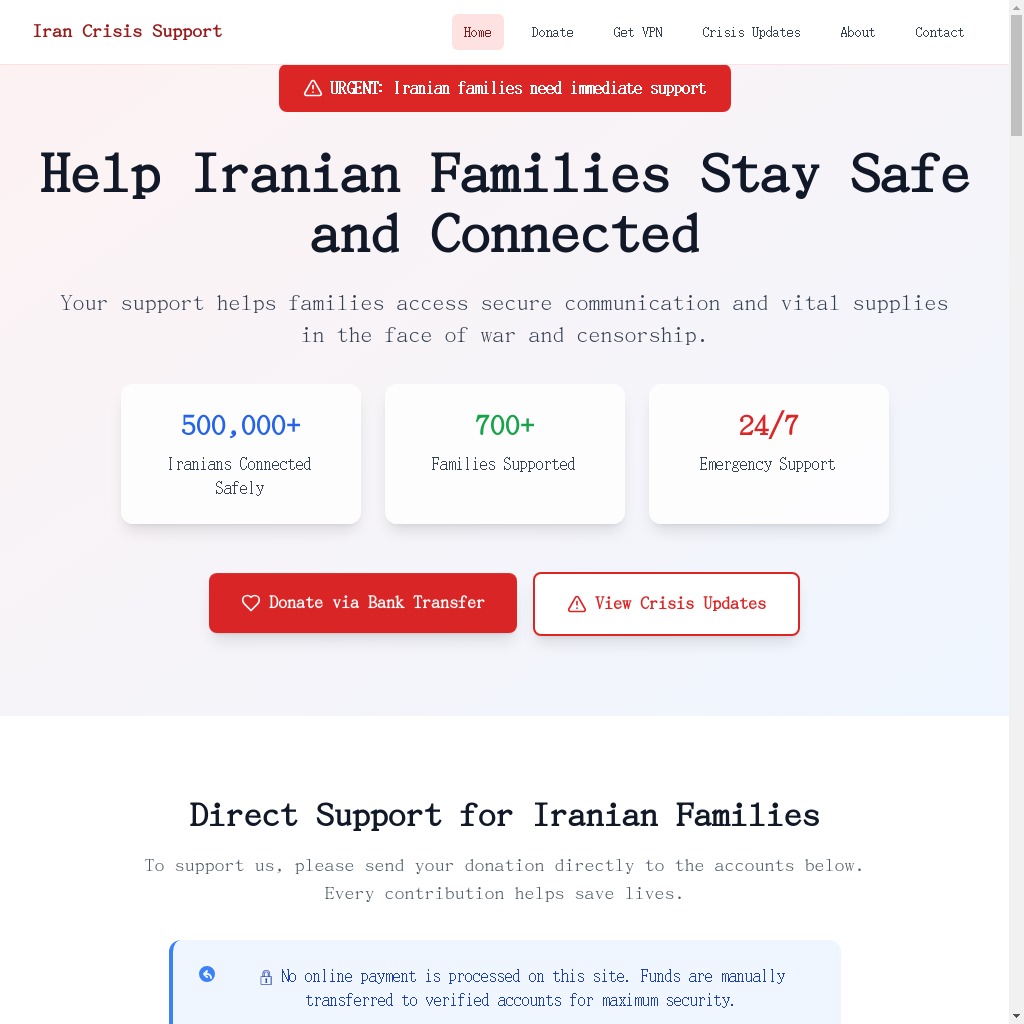
Attackers have registered new conflict-themed domains, numbering in the thousands. They are being used for malicious purposes, including creating fake storefronts, running donation scams and hosting phishing portals. Screenshots of these domains are shown in Figures 1-3.
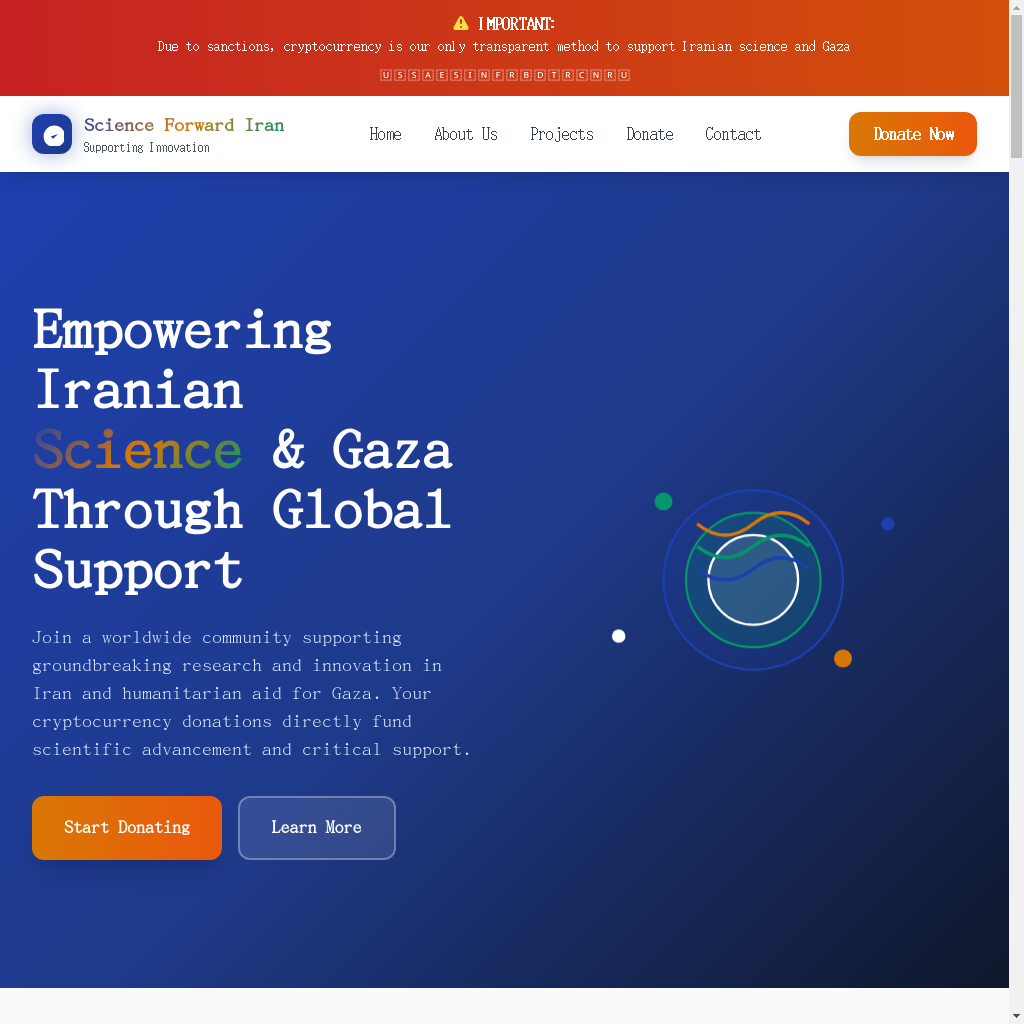
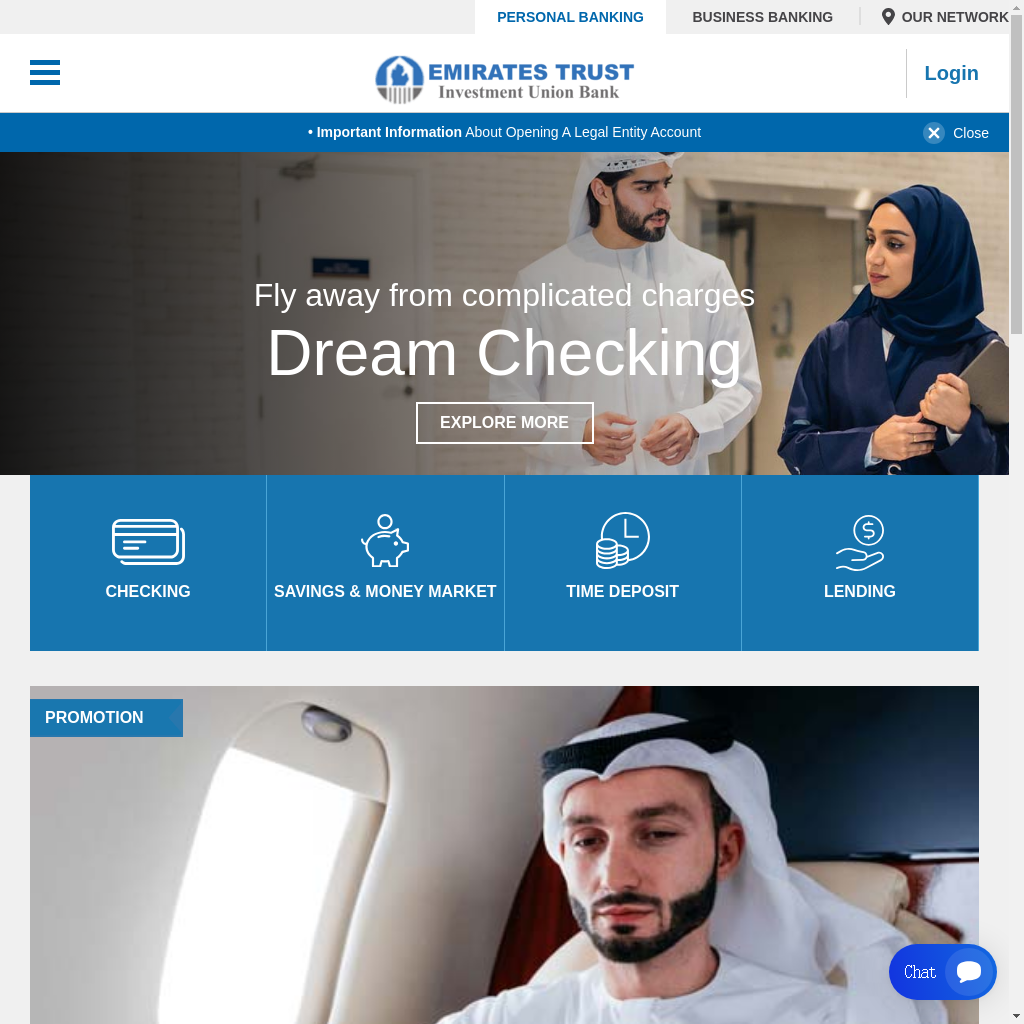
Emirates-Focused Crypto and Financial Fraud
Palo Alto Networks has identified two separate malicious campaigns targeting people in the United Arab Emirates (UAE).
- One campaign involves financial fraud exploiting brands with “Emirates” in the name.
- The second consists of crypto and investment scams using domains branded with the word “Dubai,” which leverage lures related to high-value real estate and luxury lifestyles.
Figures 3 and 4 below show examples of scam domains for asset management and banking.

Targeted Regional Enterprise Impersonation
We’ve observed two campaigns targeting a regional telecommunication brand corporate portal with impersonation, using a fake dialing-code prefix to replicate the company’s enterprise portal. We also identified a billing fraud campaign masquerading as the same company. These attackers registered the same domain concept across multiple top-level domains, rotating as each is blocked.
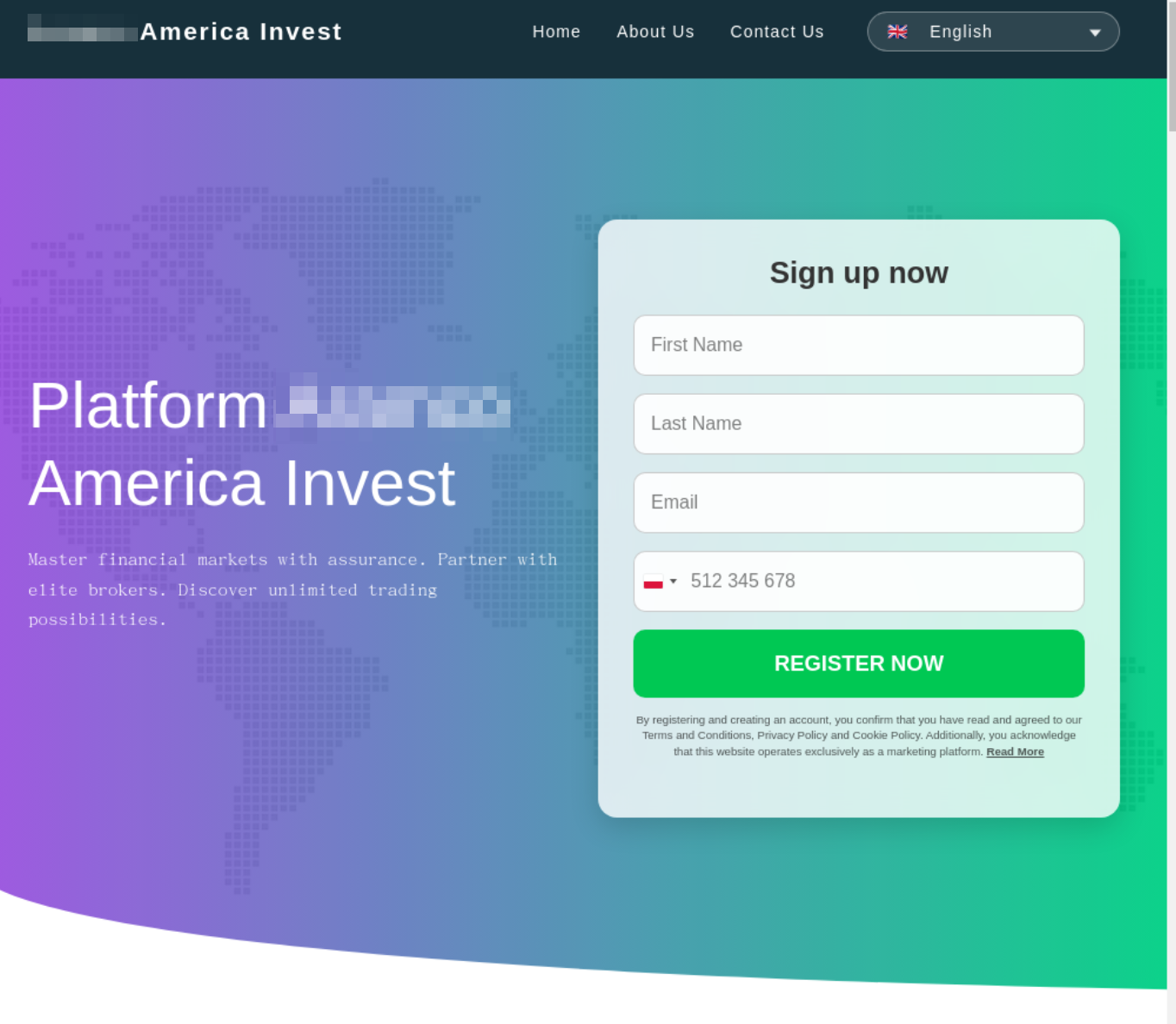
We are tracking a wave of targeted attacks against leading organizations in Saudi Arabia. The attackers are deploying a dual-pronged strategy:
- Highly tailored enterprise credential phishing that mimics major enterprise resource planning (ERP) brands to trick employees
- Widespread financial fraud
These broader schemes are designed to trap both employees and consumers using the following:
- Malicious utility billing portals
- Corporate-branded investment scams
- Misspelled banking sites leveraging Outlook subdomain chaining to deceive victims (Figure 5 shows an example of this type of scheme)
Opportunistic Criminal Credit Card Theft
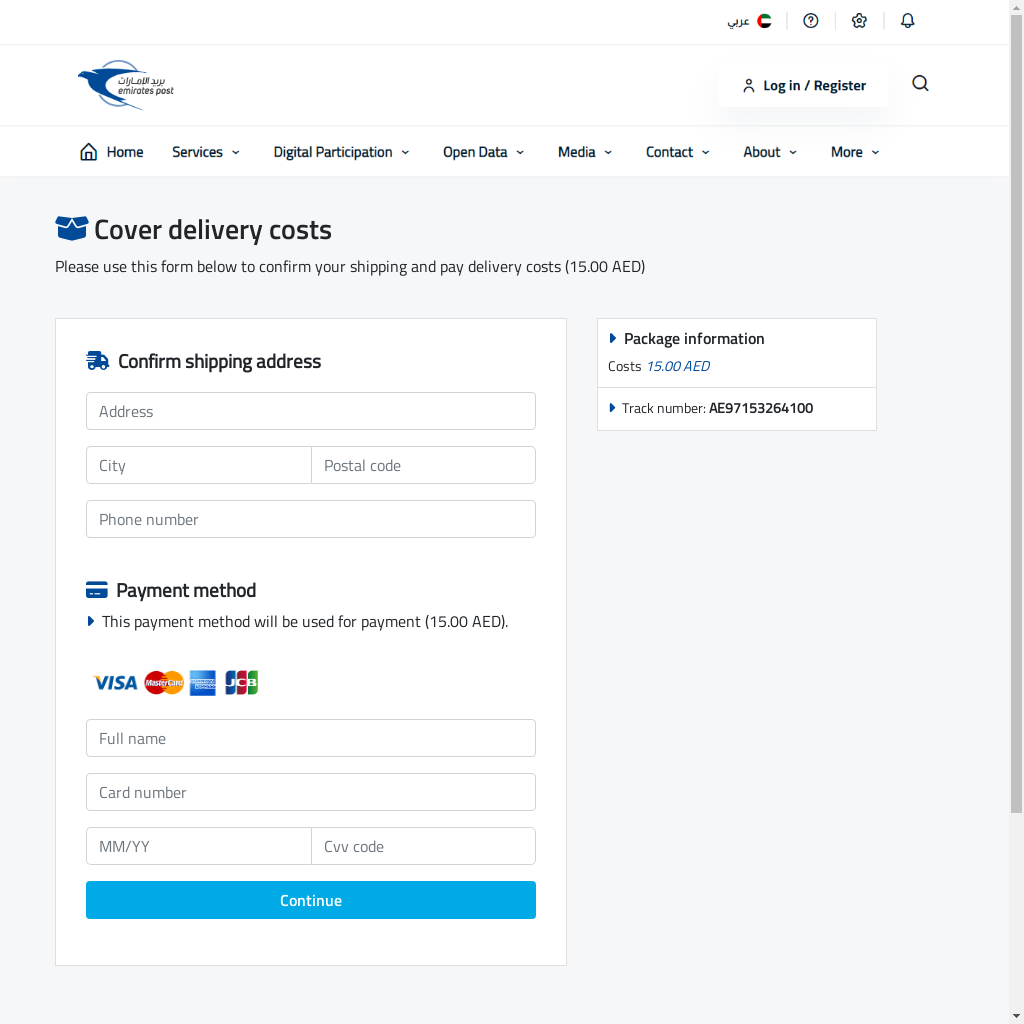
Attackers are luring users to fraudulent payment pages that mimic legitimate package delivery services to steal credit card credentials. These malicious sites are characterized by using newly registered domains and generic hosting domains, frequently incorporating Emirates Post within the subdomain.
A key technical detail is attackers using the cdn-cgi/phish-bypass path on certain domains, such as traz[.]top. This path indicates a specific tactic designed to exploit and circumvent security challenges. Figure 6 below shows an example.
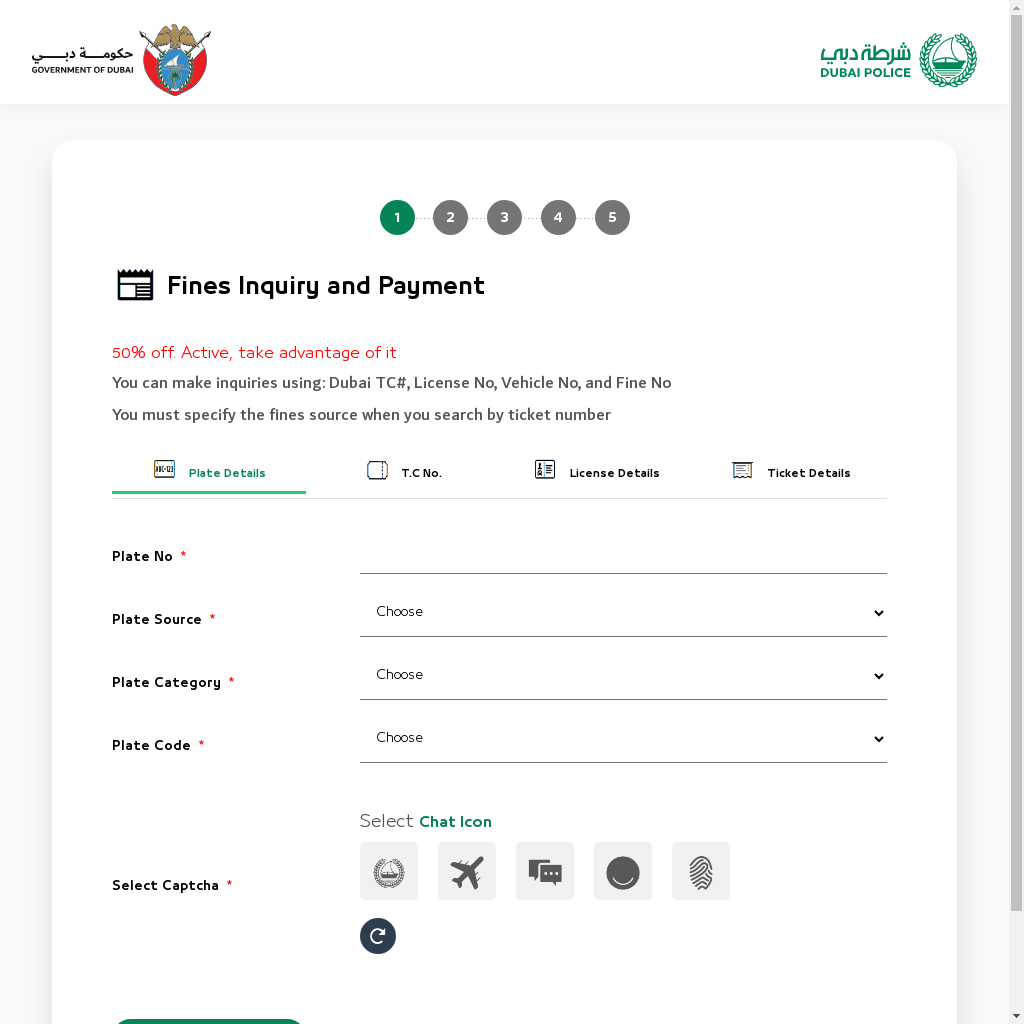
Impersonation of Dubai Government Authorities
In another financially motivated campaign, attackers impersonated legitimate government entities for credit card theft. Specifically, we discovered the path payment-system/card-process?amount=125 on a domain designed to mimic a fine payment flow, as shown in Figure 7.
Iranian Bank Masquerading
Attackers are impersonating Iranian banks to manipulate victims into supplying banking credentials. We identified three domains impersonating Iranian banking brands. One domain uses an unconventional gambling top-level domain (TLD), suggesting difficulty in registering a traditional country code TLD (ccTLD). Another domain directly exposes a payment form via the /payment-form/ path.
Iran Targeting
We identified a campaign misusing the name of Iran's largest mobile operator as the registrable domain, then embedding a convincing Microsoft URL chain in the subdomain labels to impersonate a Microsoft account recovery page.
Two identified domains use a technique that embeds globally recognized and trusted brands as subdomains within a Middle East-branded malicious registrable domain. This exploits a user's left-to-right reading pattern, presenting the legitimate brand name first. This method is effective as it doesn't require typosquatting, because the real brand name is used exactly.
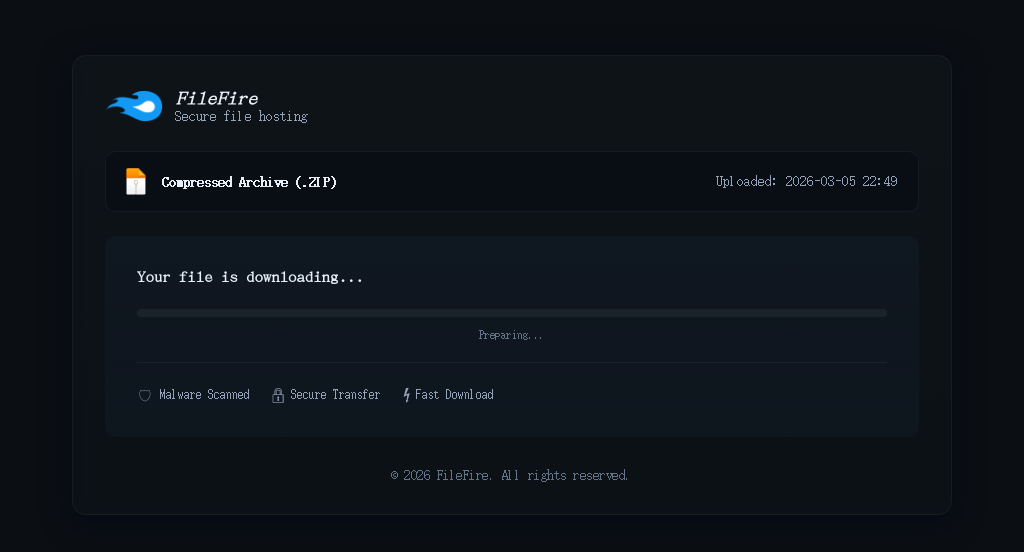
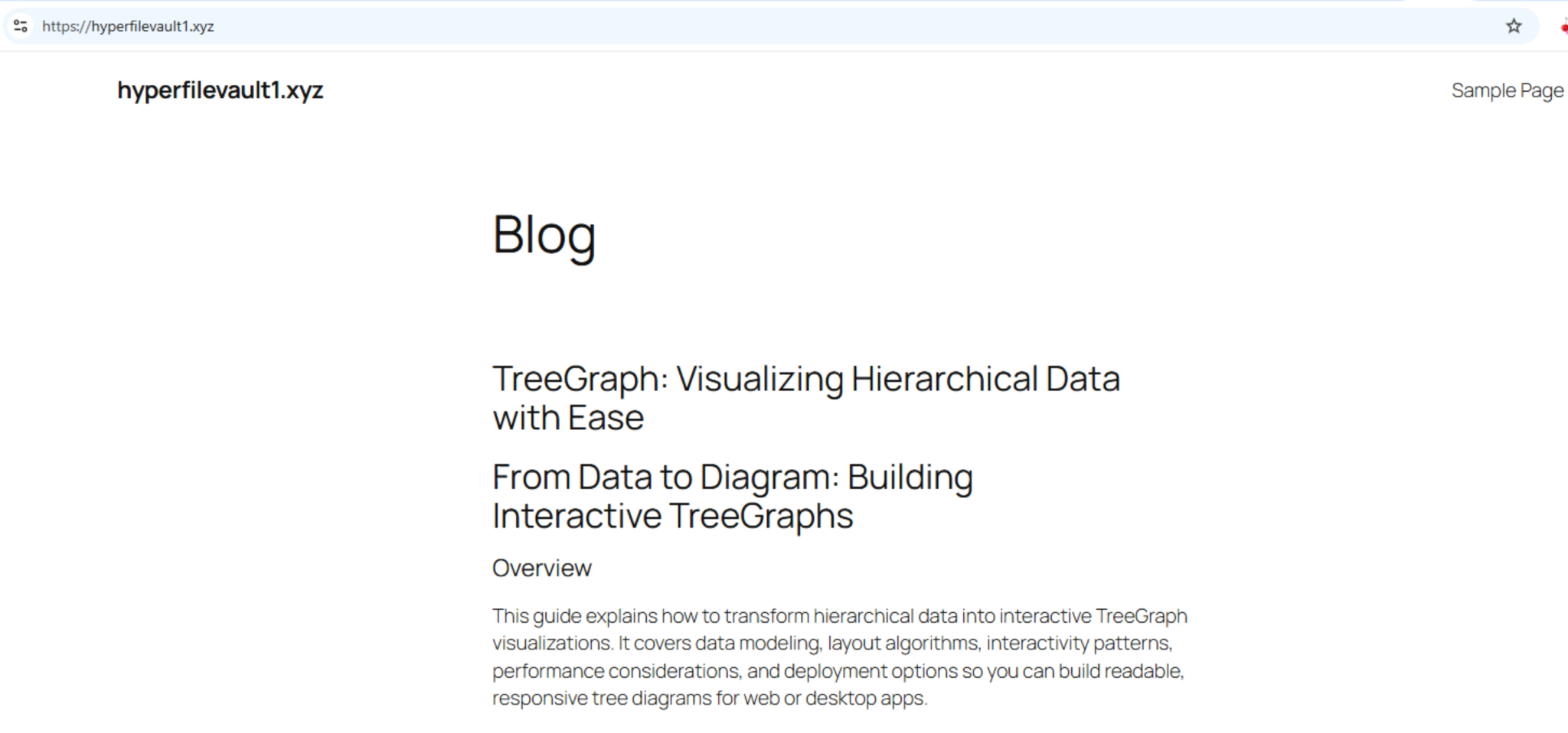
StealC Infostealer Infrastructure
Our analysis of reported StealC infrastructure revealed additional infrastructure and suggests that the attackers are using a numbered-increment pattern across identical top-level domains. This is likely an evasion tactic, where attackers register a new, incremented domain whenever the previous one is blocked.
The attack flow involves a malicious JavaScript that redirects victims to a file-hosting page, which then delivers the StealC payload within a password-protected ZIP archive. Additional examples of these file-hosting pages are shown below in Figures 8 and 9.
Earlier Threat Activity Since February 2026
Unit 42 has identified an active phishing campaign using a malicious replica of the Israeli Home Front Command RedAlert application. This campaign weaponizes a legitimate-looking Android package (APK) to deliver mobile surveillance and data-exfiltrating malware (Figure 10).
We have also observed a surge in hacktivist activity, with some estimates of 60 individual groups active, including pro-Russian groups as of March 2, 2026. Multiple Iranian state-aligned personas and collectives have claimed responsibility for a range of disruptive operations, several of which are associated with the recently established “Electronic Operations Room” formed on Feb. 28, 2026. Key observed entities include:
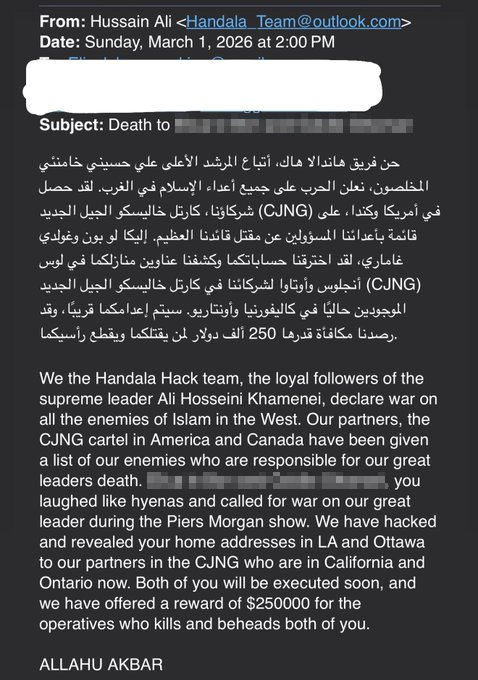
- Handala Hack, a hacktivist persona linked to Iran's Ministry of Intelligence and Security (MOIS), is the most prominent Iranian persona. The persona blends data exfiltration with cyber operations against the Israeli political and defense establishment.
- APT Iran, a pro-Iranian hacktivist collective that has gained notoriety for its hack-and-leak operations
- The Cyber Islamic Resistance, a pro-Iranian umbrella collective that coordinates multiple hacktivist teams — including groups like RipperSec and Cyb3rDrag0nzz — to launch synchronized DDoS attacks, data-wiping operations and website defacements against Israeli and Western infrastructure
- Dark Storm Team (also known as DarkStorm or MRHELL112) is a pro-Palestinian and pro-Iranian collective that specializes in large-scale DDoS and ransomware
- Claimed to have targeted several Israeli websites, including an Israeli bank in DDoS attacks
- The FAD Team (often referred to in reports as the Fatimiyoun Cyber Team or Fatimion) is composed of pro-regime actors who focus on wiper malware and permanent data destruction
- Claimed responsibility via their public Telegram board for gaining unauthorized access to multiple SCADA/PLC systems in Israel and other countries
- Claimed responsibility via their public Telegram board for gaining unauthorized access to control systems associated with more than 24 private devices belonging to an Israeli security services company
- Conducted an attack against a Turkish media outlet
- Evil Markhors is a pro-Iranian group typically specializing in credential harvesting and identifying unpatched critical systems
- Claimed responsibility via their public Telegram board for targeting an Israeli bank website
- Sylhet Gang (often cited as Sylhet Gang-SG) acts as a message amplifier and recruitment engine for the pro-Iranian hacktivist front and participates in DDoS attacks
- Claimed responsibility via their public Telegram board for targeting the Saudi Ministry of Home Affair's HCM and Internal Management Systems
- 313 Team (Islamic Cyber Resistance in Iraq), is an active pro-Iranian hacktivist cell
- DieNet is a pro-Iran hacktivist group conducting DDoS attacks on various organizations across the Middle East
- Claimed responsibility for attacking an airport in Bahrain
- Claimed responsibility for attacking Sharjeh Airport in Saudi Arabia
- Claimed responsibility for targeting Riyadh Bank website
- Claimed responsibility via their public Telegram board for targeting the Bank of Jordan
- Claimed responsibility via their public Telegram board for targeting an airport in the United Arab Emirates
The group Handala Hack also reportedly targeted an Iranian-American and Iranian-Canadian influencer with direct death threats via email (shown in Figure 11), claiming to have leaked their home addresses to physical operatives in their respective home locations.
This type of action represents an escalation of threatening cyber activity directed toward perceived critics of Iran.
Other Threat Group Activity
Cybercriminals are reportedly capitalizing on the conflict by targeting individuals in the United Arab Emirates via a social engineering vishing scam to steal credentials. The threat actors call potential victims impersonating the Ministry of Interior, claiming to be confirming receipt of a national alert and prompting for the victim’s Emirates Identification Number (EID) for verification.
The ransomware-as-a-service (RaaS) group Tarnished Scorpius (aka INC Ransomware) has listed on its leak site an Israeli industrial machinery company, and replaced the company logo with a swastika.
Pro-Russian Hacktivist Activity
Cardinal, a pro-Russian hacktivist group, claimed to target Israel Defense Forces (IDF) systems via their public Telegram board. The group is assessed to be state-aligned but likely operates independently of direct state funding. The group claims to have infiltrated IDF networks referencing a purportedly confidential document related to “Magen Tsafoni” (Northern Shield). The posted document includes operational movement details, command approvals and contact information.
The pro-Russian hacktivist group NoName057(16) has claimed multiple Israeli targets including disruptive operations against a range of Israeli municipal, political, telecom and defense-related entities.
The pro-Russian hacktivist collective “Russian Legion,” claimed to have access to Israel’s Iron Dome missile defense system. In their post, they claimed to be controlling radars, intercepting targets and monitoring in real-time, with reported system paralysis and loss of interception control. The group also claimed a new cyber operation it says compromised closed IDF servers.
State-Sponsored Attacks
Unit 42 tracks various Iranian state-sponsored actors under the constellation name Serpens. These groups could increase or escalate activity in the coming weeks.
State-sponsored Iranian cyber capabilities are often used to project and amplify political messaging (often using destructive and psychological tactics). These efforts are likely to focus on regional targets (e.g., Israel) as well as what they deem high-value targets (e.g., politicians, key decision-makers and other directly involved entities).
State-sponsored campaigns might target their victim’s supply-chains, critical infrastructure, vendors or providers.
Conclusion
Given the rapidly changing nature of this situation, a multi-layered defense is most effective as no single tool can provide complete protection. We recommend focusing on foundational security hygiene, a proven approach that provides resilient protection against a wide range of tactics.
We recommend taking the following precautions to help mitigate the impact from possible attacks. These recommendations are consistent with previous guidance provided.
Tactical Recommendations
- Ensure at least one copy of critical data is stored offline (air-gapped) to mitigate against encryption or deleting backups stored on the network
- Implement strict “out-of-band” verification for incoming requests via media, verifying through a separate trusted corporate channel
- Increase response to any threat signals where possible, especially those associated with internet-facing assets such as websites, virtual private network (VPN) gateways and cloud assets
- Ensure internet-facing infrastructure is up to date with security patches and other hardening best practices
- Train employees on phishing and social engineering tactics and continuously monitor for suspicious activity
- Consider implementing geographic IP address blocking from specific high-risk regions where legitimate business is not conducted
- Have a robust communications plan ready to address unauthorized access versus system compromise, as hacktivist groups often exaggerate their reach. Scoping and quickly verifying the potential compromise can prevent public panic.
- Continue to check for updates from trusted cyber agencies such as the UK National Cyber Security Center and the U.S. Cybersecurity and Infrastructure Security Agency (CISA) Iran Threat Overview and Advisories page
Strategic Recommendations
- Begin or update business continuity plans for any staff or assets that digital or physical attacks could disrupt
- Prepare to validate and respond to claims of breaches or data leaks
- Threat actors might use claims (even if they’re untrue) to embarrass or harass victims, or to disseminate political narratives
As activity is likely to continue to intensify throughout the duration of these events, it’s important to remain vigilant to potential attacks. Hacktivists and state-supported threat actors have been opportunistic, leading to potentially unexpected sources being targeted.
We will update this threat brief as more relevant information becomes available.
How Palo Alto Networks and Unit 42 Can Help
Palo Alto Networks customers can leverage a variety of product protections and updates to identify and defend against threats related to aspects of these events.
If you think you might have been compromised or have an urgent matter, get in touch with the Unit 42 Incident Response team or call:
- North America: Toll Free: +1 (866) 486-4842 (866.4.UNIT42)
- UK: +44.20.3743.3660
- Europe and Middle East: +31.20.299.3130
- Asia: +65.6983.8730
- Japan: +81.50.1790.0200
- Australia: +61.2.4062.7950
- India: 000 800 050 45107
- South Korea: +82.080.467.8774
Next-Generation Firewalls and Prisma Access With Advanced Threat Prevention
Advanced Threat Prevention has an inbuilt machine learning-based detection that can detect exploits in real time.
Cloud-Delivered Security Services for the Next-Generation Firewall
Advanced URL Filtering and Advanced DNS Security identify known URLs and domains associated with this activity as malicious.
Cortex
Cortex XDR, XSIAM and Cortex Cloud are designed to prevent the execution of known malicious malware. It is also designed to prevent the execution of unknown malware and other malicious activities using Behavioral Threat Protection and machine learning based on the Local Analysis module.
Additional Resources
- Iranian Cyber Threat Evolution: From MBR Wipers to Identity Weaponization – Unit 42, Palo Alto Networks
- Insights: Increased Risk of Wiper Attacks – Unit 42, Palo Alto Networks
- Boggy Serpens Threat Assessment – Unit 42, Palo Alto Networks
Indicators of Compromise
- hxxps[:]www[.]shirideitch[.]com/wp-content/uploads/2022/06/RedAlert[.]apk
- hxxps[:]//api[.]ra-backup[.]com/analytics/submit.php
- hxxps[:]//bit[.]ly/4tWJhQh
- media.megafilehost2[.]sbs
- cache3.filehost36[.]sbs
- alpha.filehost36[.]sbs
- srv2.filehost37[.]sbs
- arch2.megadatahost3[.]homes
- media.hyperfilevault2[.]mom
- hyperfilevault2[.]mom
- www.hyperfilevault2[.]mom
- arch2.maxdatahost1[.]cyou
- hyperfilevault1[.]xyz
- hyperfilevault3[.]mom
- hyperfilevault3[.]pics
- pnd.86c.mytemp[.]website
- d1g.ccd.mytemp[.]website
- s0u.210.mytemp[.]website
- 2pd.f22.mytemp[.]website
- eg3.db1.mytemp[.]website
- f43.c76.mytemp[.]website
- kzw.ce3.mytemp[.]website
- c45.94b.mytemp[.]website
- kmd.8cd.mytemp[.]website
- c1y.bf3.mytemp[.]website
- m1w.4a0.mytemp[.]website
- njb.551.mytemp[.]website
- 2b1.916.mytemp[.]website
- 92j.130.mytemp[.]website
- b1z.0f6.mytemp[.]website
- b0p.c0d.mytemp[.]website
- nxj.e57.mytemp[.]website
- pro.iranpanel[.]life
- www.iran2026[.]org
- iranpaye[.]com
- www.forever-iran[.]net
- irandonation[.]org
- irancross[.]shop
- aramcoamericainvest[.]com
- trumpvsirancoin[.]xyz
- iran[.]drproxy[.]pro
- iran2[.]drproxy[.]pro
- iran11[.]drproxy[.]pro
- iran14[.]drproxy[.]pro
- iran15[.]drproxy[.]pro
- iran16[.]drproxy[.]pro
- iran18[.]drproxy[.]pro
- iran19[.]drproxy[.]pro
- tehran[.]t2.drproxy[.]pro
- emiratesinvestunion[.]com
- buydubaipropertywithcrypto[.]com
- cryptocurrencies-offers[.]com
- the-dubai-lifestyleapp.cryptocurrencies-offers[.]com
- emiratescryptobank[.]com
- secretemirates[.]com
- emiratespost-pay[.]com
- ae-payapp[.]com
- www.emirates-post[.]ae-payapp[.]com
- traz[.]top
- emiratespost[.]traz[.]top/cdn-cgi/phish-bypass?atok=
- racunari-bl[.]com
- emirates-post[.]racunari-bl[.]com/en/card.php
- myemiratespost[.]click
- emirates-ae[.]pack-541202699[.]azmtrust[.]com
- portal[.]sapb-aramco[.]com
- cnmaestro[.]sapb-aramco[.]com
- saudi-bill-pay[.]com
- saudidigtalbank[.]com
- outlook[.]outlook[.]saudidigtalbank[.]com
- aramcoamericainvest[.]com
- dubaicustonms[.]top
- dubai-custboms[.]top
- dubai-custbims[.]top
- dubai-customs[.]top
- dubaicustoms[.]top
- dubaicuctoms[.]com
- dubaiicuctoms[.]com
- gov-tollbillba[.]life
- com-govauv[.]top
- dubaipolice[.]gov-tollbillba[.]life
- dubaipolice[.]com
- govauv[.]top
- portal[.]0111etisalat[.]com
- www[.]portal[.]0111etisalat[.]com
- superset[.]0111etisalat[.]com
- www[.]superset[.]0111etisalat[.]com
- yoshi[.]0111etisalat[.]com
- _dmarc[.]www[.]portal[.]0111etisalat[.]com
- etisalatquickpay[.]com
- etisalataccountquickpayae[.]top
- etisalataccount-quickpayae[.]click
- cover[.]www[.]microsoft[.]com[.]irancell[.]courses
- recovery[.]cover[.]www[.]microsoft.com[.]irancell[.]courses
- bankofamerica[.]com[.]oidscreen[.]gorequestlocale[.]emiratesbankgroup[.]info
- appleid[.]apple[.]com-update[.]required[.]kontol[.]emiratesbankgroup[.]info
- store[.]appleid-apple[.]com-confirmation[.]verif[.]emiratesbankgroup[.]info
- bankiran[.]bet
- irandargah[.]com
- iransupports[.]cyou
- iransupporttyst[.]cyou
- iransupasdports[.]cyou
- iransusdpportsdf[.]cyou
- firansupport[.]cyou
- kiransupport[.]cyou
- trdfiransupport[.]cyou
- airansupasdports[.]cyou
- biransupasdports[.]cyou
- kiransupportsdf[.]cyou
- fkiransusdpportsdf[.]cyou
- sffifdsfsransupasdports[.]cyou
- portal.0111etisalat[.]com
- superset[.]0111etisalat[.]com
- yoshi[.]0111etisalat[.]com
- _dmarc[.]www[.]portal[.]0111etisalat[.]com
- etisalatquickpay[.]com
- etisalataccountquickpayae[.]top
- etisalataccount-quickpayae[.]click
Updated March 23, 2026, at 3:30 p.m. PT to add Additional Resources section.
Updated March 26, 2026, at 2:00 p.m. PT to add information on conflict-themed phishing lures.










 Get updates from Unit 42
Get updates from Unit 42